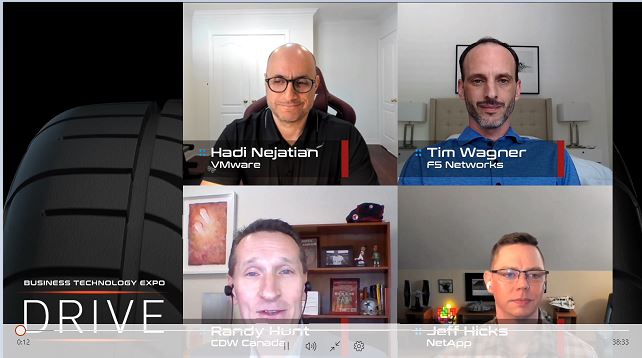
At CDW’s BTEX 2021 virtual event, Solution Architect Randy Hunt led a panel discussion that looked into the findings of CDW Canada’s 2021 Cloud Report, and other important trends in the hybrid cloud. Here are some of the highlights of their discussion.
How to stay on track with hybrid cloud innovation
“What I hear a lot with customers is the term ‘cloud-native,’ and people think that means cloud-provider created products,” says Tim Wagner, Cloud Evangelist, F5 Networks. “But really, it’s about a philosophy and a mentality. So, if we want to keep up with the pace of change, we have to put ourselves in the right mindset to look at business outcomes.” This can be broken down into three questions:
- What are we after?
- What principles do we have before we’re going to put something out?
- How do we enable our dev teams to run at the speed of business?
By keeping these questions in mind, organizations can start to naturally develop patterns that can help them keep pace, and aid in product selection.
“Going cloud-native is truly a monumental challenge,” says Jeff Hicks, Hybrid Cloud Solution SE, NetApp. “It’s not something an organization can adopt overnight. You have to first be introspective about your skill set, and then be introspective about what makes your business unique. Those are the areas you need to then invest in.”
Oftentimes, moving everything into the public cloud too quickly can lead to regrets. The CDW Cloud Report mentions that 86 percent of organizations that move to the cloud will repatriate some workloads due to security, performance and cost.
“Because if you rush to it, and don’t have the principles, then you look at your bill a year later and panic,” says Wagner. “You need to go slow to go fast.”
Wagner also compares moving to the cloud to a home renovation, with an example about having the right infrastructure in place. “Everybody wants to talk about the cool kitchen faucet, but if you don’t put the plumbing behind the walls to make sure the water can get there, it doesn’t matter how great that faucet is.”
How to include cloud, microservices and DevOps in an application modernization strategy
“App modernization is a two-for-one approach,” says Hadi Nejatian, Staff Cloud Partner Solution Architect, VMware. “On one side we have the development team that wants to launch and develop their applications as fast as they can. On the other side, the operations team wants to have an operational point of view around all the implementations that the dev team makes.”
So, how can you get those teams working together? Nejatian says “Give both developers and operations the tools to make sure they can develop those apps as fast as they can.”
“Alignment is critical,” says NetApp’s Jeff Hicks. “Teams have to work together well, and I think that is no small feat, getting teams that are taking a legacy approach to work together with the people you’ve tasked to modernize applications.” For Hicks, this requires finding someone in the organization to champion app modernization, and having them do their research. “Find out what are the technologies in this space that are going to be an advantage to your digital transformation strategy.”
“What’s often missed is you have to work to remove bias,” adds Hicks. “When you task a team to do a certain thing, they tend to fall in love with it. And that becomes all they want to do. You’ve got to invest in getting people familiar with processes, but also help them understand that ‘I need you to champion this, but don’t get married to it, because we might be changing direction in a few months.’”
Innovative use cases in IT orchestration and automation
F5’s Tim Wagner actually mentions NetApp’s CloudOne platform as a great example. “I think what they’re doing is super-important, building the platform and setting those guide rails for the developers to run and everybody in IT Ops knows what it is. It’s a really smart approach.”
From an F5 perspective, Wagner is focused on the security aspect. “One of them being SSL certificates, and managing expiration periods. How can we automate that process, and actually make security less the ‘Group of No’ and more the group of ‘Let’s Go’?”
“Some call it Shift Left, I call it Shift Smarter,” he continues. “Which is simply ‘How can I do the remedial tasks efficiently?’ And certificates is a key one that enables most of the things happening on the internet today.”
VMware’s Hadi Nejatian points to infrastructure as code as a good example of automation. “If you’re coming from an IT department, one of your main consumers is the app developers. When you talk to them, you realize when they’re developing code for their apps, they don’t want to deal with the infrastructure components that their applications run on – routers, cables, etc. Therefore, if you’re able to provide them infrastructure where they can simply put in one line of code, start running it and get what their applications need, that really gives you the benefit of keeping those customers happy, while giving them the agility they’re looking for.”
F5’s Wagner also offered a suggestion for BTEX attendees. “Pick one task that you do every day of the week, and automate that task. One automation will turn into two, two turns into four, and you start to get that scale pretty rapidly.”
Is the cloud more secure or less secure than an on-prem data centre?
“The last I checked, there were a lot of breaches before cloud existed,” says Wagner. “There are still a lot of breaches. So it feels like a false premise to me.”
Wagner notes that major cloud providers like Microsoft, Amazon and Google spend a lot of money securing their infrastructure, but it all comes down to the cloud user’s applications. “I see all the buzzwords around zero-trust, and secure access, but it all comes back to principles and having design based in reality for your application. No, you’re never going to outsource security, but security policy is much different than ‘Let’s just buy a bunch of tools and hope they solve the problem.’”
Even as an employee of a security vendor, Wagner admits that no vendor can solve all security-related problems. “Good policy, good principles and understanding where your risk lies to the data is what matters when you go to the cloud.”
“As we have people evolving into hybrid cloud and embracing digital transformation, we know that security is top of mind,” says Hicks from NetApp, who mentions three dynamics in play:
- Cloud security vs. internal security – which one is better? Trying to keep up with threats, hackers and attacks can often cause burnout, and introduce security gaps in your environment.
- The cloud is a bigger target. If attackers can breach a major public cloud provider, they now have access to much more information, disrupting many more environments in the process, whereas a smaller organization might not be targeted otherwise.
- Defending the transport layer. This is when your data is exposed to the world, so what are you doing to secure those gateways, or encrypt data in flight?
At the end of the day, Hicks recommends a layered security posture. “You can’t just have perimeter defence, or defence at your data layer. You have to have it throughout. As you adopt a hybrid cloud strategy, and regardless of where your data lives – in the public cloud, in your data centre or in transit – you need to have a security posture that’s executed across all of those locations.”
How has the evolution of the threat landscape impacted migrations to the cloud?
“If you look at public cloud providers, they are highly secure environments,” says VMware’s Nejatian. “The challenge that customers have is that they’re running workloads in multicloud environments. Each of these cloud environments, although they are highly secure, they each have their own method of applying security, so the way that you secure workloads on each of them is different.”
“Each of these environments are vertically integrated silos,” Nejatian continues. “They have highly integrated services that are vertically working with each other, but with less horizontal capabilities across other clouds. That makes it challenging for customers.”
The challenge of misconfiguration or under-configuration arises when trying to apply various vendors’ security policies across different workloads to keep them secure and protected. “Security has to be with your workload everywhere it goes,” says Nejatian. “You want to make sure you have a consistent security policy; define once and repeat multiple times.”
“Security is a responsibility of everyone involved in the data pipeline,” says NetApp’s Hicks. “There’s a learning curve and an expertise required for each of the public clouds, but there’s also a heightened individual responsibility when you’re operating in those public clouds. It’s not just your data that you’re potentially putting at risk when you’re being irresponsible in those environments.”
“As a community, we can come together and work harder to standardize policies, practices and tool sets. But in the meantime, every organization has to know what is important to them, what those polices are and ensure that they’re adhered to across the data pipeline.”
F5’s Wagner says the one thing he would do if going to the cloud, regardless of vendor or technology, is to start adding context to data access and clamping down on identity. “Identity is the key to all future cloud security parameters because the perimeter is going to evaporate” as organizations move more data to the edge.
For more insights from the CDW Cloud Report, you can download the report now. And be sure to bookmark this page for more coverage of BTEX 2021.