Whether you own a small business, manage a busy branch location, or run a large department, you can count on HP for secure, dependable, and cost-effective printers to meet your needs. CDW and HP allow businesses to focus on and manage their business, not printers.

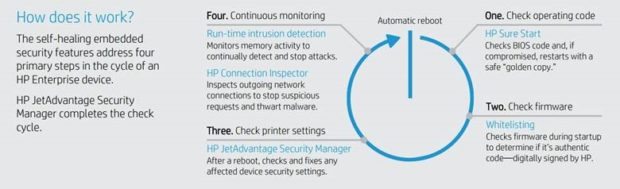
HP printers have the industry’s strongest security, with four key technologies that are always on guard, continually detecting and stopping threats while adapting to new ones. Only HP Enterprise printers automatically self-heal from attacks by triggering a reboot—IT doesn’t need to intervene.
After a reboot occurs, HP JetAdvantage Security Manager automatically assesses and, if necessary, remediates device security settings to comply with pre-established company policies.
HP Sure Start—checks operating code
The BIOS is a set of boot instructions used to load critical hardware components and initiate firmware. HP Sure Start technology works behind the scenes by validating the integrity of the BIOS when powering up. If a compromised version is discovered, the device restarts using a safe “golden copy” of its BIOS.
Whitelisting—checks for authentic firmware, digitally signed by HP
Because compromised firmware could expose your whole network to an attack, whitelisting helps ensure the code that coordinates your printer’s functions, controls, and security hasn’t been tampered with. Firmware is automatically checked during startup, and if an anomaly is detected, the device reboots to a secure, offline state and notifies IT.
Run-time intrusion detection—monitors memory activity
HP’s run-time intrusion detection helps protect printers while they are powered on and connected to the network—right when most attacks occur. This technology checks for anomalies during complex firmware and memory operations, automatically stops the intrusion, and reboots.
HP Connection Inspector—inspects network connections
Stop malware from “calling home” to malicious servers, stealing data, and compromising your network. HP Connection Inspector evaluates outgoing network connections to determine what’s normal, stop suspicious requests, and automatically trigger a self-healing reboot.
The role of IT is evolving. Across industries, in organizations large and small, IT is being asked to solve organizational challenges, not just tech challenges. Doing so requires a broader focus that brings together different technologies in support of the same goal. It requires IT Orchestration by CDW.
Let CDW and HP Make IT Purchasing Easy for your business – Contact your CDW account manager today!






